Technical Defenses - Part I
"It's an old story: protecting against the rare and spectacular by making yourself more vulnerable to the common and pedestrian." - Bruce Schneier
Nothing works more in a thief’s favor than people feeling secure. That’s why places that are heavily alarmed and guarded can sometimes be the easiest targets. The single most important factor in security -- more than locks, alarms, sensors, or armed guards -- is attitude. A building protected by nothing more than a cheap combination lock but inhabited by people who are alert and risk-aware is much safer than one with the world’s most sophisticated alarm system whose tenants assume they’re living in an impregnable fortress.
Bill Mason, “Confessions of a Master Jewel Thief”
When I was working on my cell biology degree, I remember reading that by weight, the amoeba - a single cell organism with the ability to change shape and move about - was the most aggressive critter on the planet. All this supposed aggression focused on the pursuit of a single goal: FOOD!
And so it goes on up the food chain. Ever more complex life forms evolved the means to either turn some other critter into lunch or avoid becoming some other critter’s lunch. We humans aren’t generally interested in consuming each other, but there is a definite element to human nature that’s intent on taking each other’s rice bowl. The arrival of the Information Age has put considerable stress on the tools evolution has provided us for defending against any would-be rice bowl thieves. Most of the threats to our resources come from abstract rather than physical sources and relying on the wetware that drives the gray potato between our ears to stay on top of any scams engineered to deprive us of hard-won resources often proves inadequate.
Imagine making yourself a sandwich and when you reach to grab a couple of slices of bread, out jumps a thief demanding all your cash. Not gonna happen, obviously. Yet this can happen to the unwary when they open their email expecting harmless slices of information they’re either interested in reading or need to know. A recent New York Times article, authored by a veteran crime reporter, describes a scam he almost fell for. It reveals how sophisticated the techno rice bowl thieves have become. The article prompted me to write about several defense strategies I have for protecting me and my family from the slice of humanity that feels entitled to my resources. For a good overview of how AI has become a force multiplier in the world on technical crime, the recently published “ScamGPT: GenAI and the Automation of Fraud“ from Data and Society provides a sobering read for the non-technical.
The first fundamental principle to my strategy is : Keep as low a profile as possible.
I work (yes, it’s actually work, unfortunately) to minimize my presence on the Web. This means I must forego many things that many people consider necessities but which are in fact conveniences. In a recent post, Seth Godin illuminates the cost of convenience:
Convenience is seductive, and we trade precious things away for it all the time.
Part of the reason it dominates our lives is that we only consider the cost once. After that, it continues to remind us of the benefits–the time and hassle and decisions we save.
But convenience can cost us. Our humanity, our health, our well-being, our connection to others and to what we truly care about.
Even if it’s a habit, it might be worth reminding ourselves of what we’ve given up in exchange.
“Work worth doing” is another way to say inconvenient.
Scammers and thieves can’t target something that isn’t there. So I don’t use Venmo or Zelle or any of the cash transfer apps. I’ve had no accounts on all the major social media platforms except LinkedIn, which I recently abandoned, and X, which I joined about a year ago. No account means there’s nothing to compromise. I can’t avoid everything, though. I have no choice when it comes to using a banking app and recently closed accounts at a second bank when they made it clear they would be charging me a fee if I didn’t use there app and log in at least once a month. When customer service is replaced by operant conditioning, I take my business elsewhere. For the banking app I do have, It’s locked down in every possible way the bank allows - obscure user name, rotating passwords, 2FA, disabled biometric logins (too easy for AI to spoof), etc. When possible, I pay with cash. I have just one credit card for all other transactions.
The second fundamental principle to my strategy is : Keep moving.
When dealing with vendors, there are few levers we can pull to reduce our exposure. We can regularly change passwords, use random character strings for user names, or only access the vendor’s website from a home computer, but beyond that we’re at the mercy of whatever security the vendor has implemented to protect their systems. The size and number of data breaches over the past ten years is such that we should just assume any information we’ve ever keyed into a web page is available for purchase, if not freely available on the Internet.
This is were my skills as a software engineer have come in handy. Over ten years ago I started work on implementing a whitelist system for email. The only email messages from vendors that make it through the gauntlet and into my inbox have been pre-approved or otherwise identified as legitimate. A piece of this system is the creation and management of email aliases - alternative email addresses that forward to a primary inbox. I’m starting to see some of the bigger services offering email aliases, however they are typically limited in number - five or ten per primary account. There’s no real reason for this limit. To date, my system manages over 600 email aliases. Of those, about 10% have been flagged has having been compromised and thus disabled.
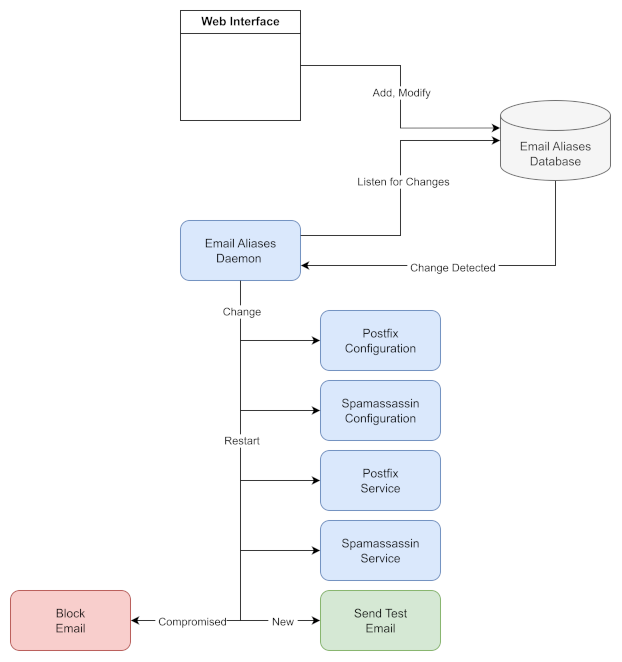
Here’s a high level view of how the system works:
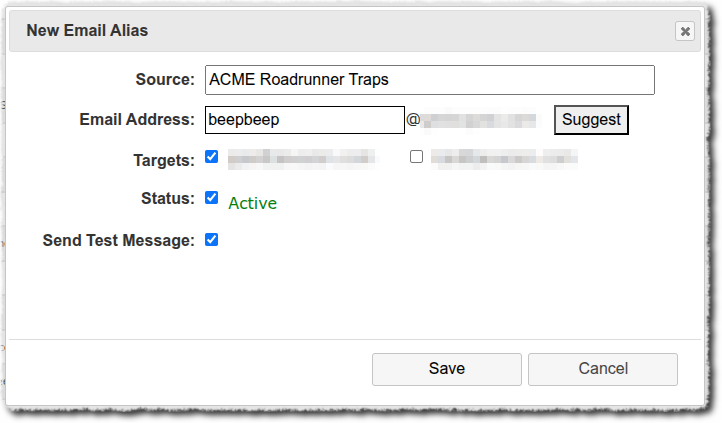
The web interface is simple and accessible only on the intranet or via a VPN connection.
The “Suggest” button generates a random email alias. When the alias is active, any messages sent to beepbeep@example.com are sent forward to one of two primary email accounts. If the status is “Inactive” any messages sent to that account are rejected by the email server. The process for activation or deactivation takes place in under 60 seconds. A unique email is set up for each vendor I do business with. If I start to receive spam on a particular vendor’s account, I know the vendor has either been hacked or my data has been sold to one or more third parties. If I have an ongoing relationship with the vendor, I change the password and email on the vendor’s account and then deactivate the old email. If there is no on-going relationship - a one-time interaction for an event registration, for example - I simply deactivate the account.
The logins for all these accounts are managed via a self-hosted instance of Bitwarden. Even though it’s locked down and buried deep within the home network, I don’t fool myself into thinking this is an impenetrable system. Just much harder to reach. There are far greater numbers of targets in the world that are much easier to find and attack.
Before implementing this system, my email server was flagging around 2,500 spam messages a day! (A consequence of having the same primary email address for the past 25 years.) If even just 1% of those messages slipped through the old system’s defenses, that’s 25 spam messages a day clogging up my inbox. Looking at the logs for the past 24 hours, the new system has dropped just 5 messages in the spam bucket.
The part I can’t see but is almost certainly happening is bad actors who are attempt to access any one of my vendor accounts with a compromised email. What makes aliases more effective then using a single primary email account is that they circumvent the bad actor’s assumption that I use the same email account for all my website logins - that is, beepbeep@example.com is probably my login for Facebook, Instagram, Big Bank, Major Shoes, Cheep Crap or any other big name vendor. When I rotate passwords, I also rotate email addresses. Scammers can knock, but chances are high nothing is listening.
There’s more to the system and strategy than this, but you probably get the picture. Email aliases along with scheduled password changes make access to my on-line accounts a moving target. Inconvenient? Perhaps. How much value do you put on peace of mind?
“Technical Defenses” last updated on 2025.10.04.
I hope you will return regularly to The Remnant’s Way as I often update posts, particularly Ab Initio, and do not always publish to email posts that are meant to support or serve as reference to existing or future posts.
And please consider becoming a paid subscriber. Doing so supports my writing efforts and grants me the most precious of all resources - dedicated time for writing. And for that, I am deeply grateful. If you prefer, buy me a cup of coffee if there is an article here and there that you enjoyed or found valuable.
Image credit: Grok 4